Validating Azure resources before moving the resources to another subscription – Part 3

In this post, we will be using Postman. You can download it from https://www.postman.com if you haven’t.
This is also where the application ID and secret that you created in Part 1 will come handy as we will be using it to generate an Auth token to perform all the steps required to validate resources in Azure.
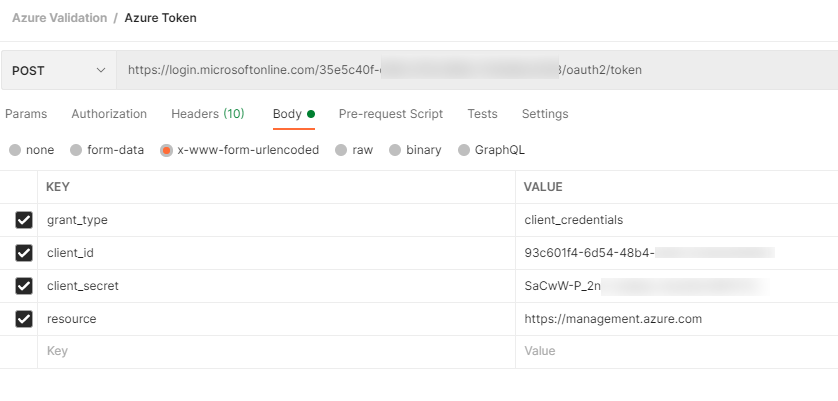
First, we will obtain the OAuth2 token by making a POST call to
https://login.microsoftonline.com/<tenantId>/oauth2/tokenusing the following values in the request body (formatted as x-www-form-urlencoded in Postman):
grant_type : client_credentials
client_id : client_id of the registered app in Part 1
client_Secret : the noted client secret in the Part 1
resource : https://management.azure.com/
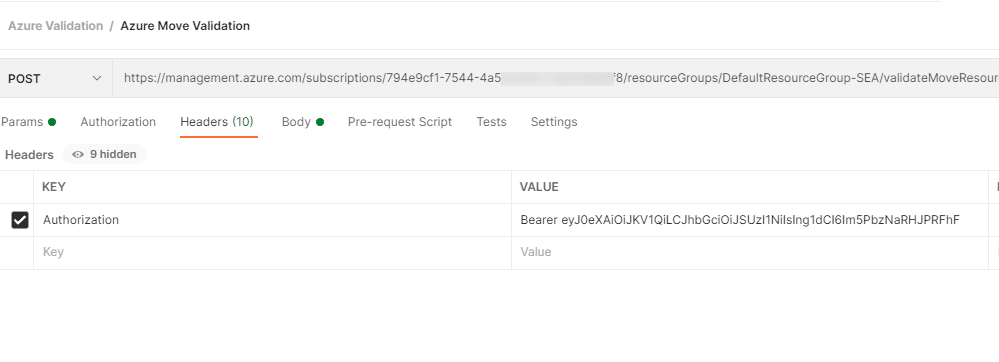
The expectation is that once you generate the token, we should be using the Bearer token option for the next request, For unknown reason, it doesn’t work for me and it kept giving me Authentication failed error. So we will be doing it different by using Authorization header instead. So make sure you note down the token as well.

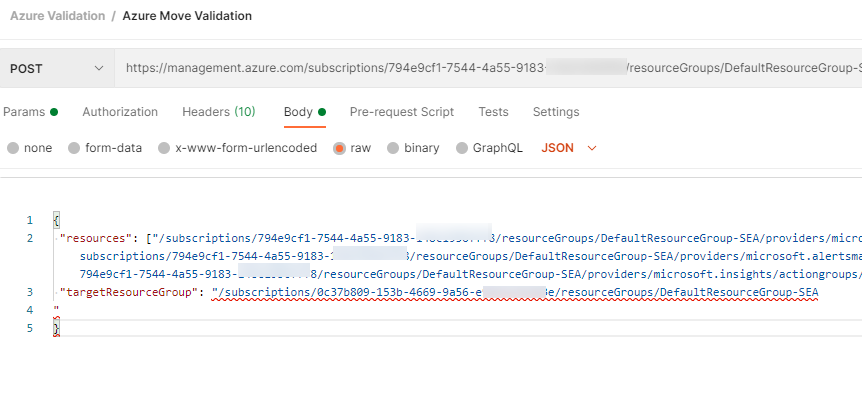
Next, we will be using all the items we’ve gotten from Part 2 to do a Post request. Refer to the latest URI from https://docs.microsoft.com/en-us/rest/api/resources/resources/validatemoveresources#uri-parameters
POST https://management.azure.com/subscriptions/{subscriptionId}/resourceGroups/{sourceResourceGroupName}/validateMoveResources?api-version=2020-06-01
For this exercise, I will be using DefaultResourceGroup-SEA as the resourcegroup. Remember to set the Authorization header and copy the oauth2 token that you’ve create in the beginning.
In the body, we will be using the following syntax. This is also where you will need to paste in the resource Ids that you’ve gotten.
{
"resources": ["<resource-id-1>", "<resource-id-2>"],
"targetResourceGroup": "/subscriptions/<subscription-id>/resourceGroups/<target-group>"
}
For mine, it would be
{
"resources": ["/subscriptions/794e9cf1-7544-4a55-9183-xxxxxxxxxx/resourceGroups/DefaultResourceGroup-SEA/providers/microsoft.alertsmanagement/smartDetectorAlertRules/Failure Anomalies - ","/subscriptions/794e9cf1-7544-4a55-9183-xxxxxxxxxx/resourceGroups/DefaultResourceGroup-SEA/providers/microsoft.alertsmanagement/smartDetectorAlertRules/Failure Anomalies - ","/subscriptions/794e9cf1-7544-4a55-9183-xxxxxxxxxx/resourceGroups/DefaultResourceGroup-SEA/providers/microsoft.insights/actiongroups/Application Insights Smart Detection"],
"targetResourceGroup": "/subscriptions/0c37b809-153b-4669-9a56-xxxxxxxxxxresourceGroups/DefaultResourceGroup-SEA
"
}
If you do this correctly, you should be getting a 202 Accepted status. This means the validation has started. Scroll down to Location and grab the URL. You will need this to get the validation result.
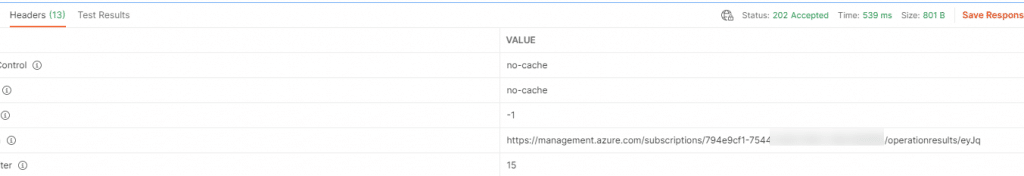
Give it about a few minutes before you do a GET using the URL that you’ve gotten from the Location field. If you get a 204 status and no errors in the Body section, that would means that validation is successful. There is no blockers that stops you from moving the resources. However, if validation fails, you will probably see something like the following
{
"error": {
"code": "ResourceMoveNotSupported",
"message": "Resource move is not supported for resource types 'Microsoft.Compute/restorePointCollections'."
}
}
"error": {
"code": "ResourceMoveFailed",
"message": "Resource move is not supported for resources that have plan with different subscriptions. Resources are 'Microsoft.OperationsManagement/solutions/Security(DefaultWorkspace-794e9cf1-7544-4a55-9183-148c1956fff8-SEA),Microsoft.OperationsManagement/solutions/SecurityCenterFree(DefaultWorkspace-794e9cf1-7544-4a55-9183-148c1956fff8-SEA),Microsoft.OperationsManagement/solutions/VMInsights(DefaultWorkspace-794e9cf1-7544-4a55-9183-148c1956fff8-SEA)' and correlation id is 'e8b269cf-865f-49c3-abb1-8ab70d39fe7e'."
}
}
{
"error": {
"code": "MultipleErrorsOccurred",
"message": "Multiple error occurred: BadRequest,BadRequest,BadRequest,BadRequest,BadRequest,BadRequest,BadRequest,BadRequest,BadRequest. Please see details.",
"details": [
{
"code": "ResourceNotTopLevel",
"message": "Identifier '/subscriptions/794e9cf1-7544-4a55-9183-148c1956fff8/resourceGroups/GROUP/providers/Microsoft.Compute/virtualMachines/WebServer02/extensions/MicrosoftMonitoringAgent' is not a top level resource."
},
Most these errors actually tells you what went wrong and what need to be fixed. So, before you actually perform any actual move/migration, trying doing a validation first. Cos this will definitely save you a lot of trouble.
Well, there you have it. Until next time~
One thought on “Validating Azure resources before moving the resources to another subscription – Part 3”